Critical security vulnerability in vCenter Server

In the week starting the sixth of April 2020 a critical security vulnerability was found in vCenter servers that were upgraded to vCenter 6.7 from previous versions like 6.0 or 6.5. On the ninth of April, VMware released a fix for this critical security vulnerability in vCenter Server 6.7. This security highlight will explain exactly what the vulnerability is, which environments are vulnerable and how to mitigate the threat.
Description
The security vulnerability is listed under CVE ID ‘CVE-2020-3952‘ and has a CVSSv3 maximum rating of 10. When an environment is impacted it means the Access Control List of the VMware Directory Service is incorrectly implemented.
VMware Says: “A malicious actor with network access to an affected vmdir deployment may be able to extract highly sensitive information which could be used to compromise vCenter Server or other services which are dependent upon vmdir for authentication.”
Environment vulnerability check
vCenter Server 6.7 (embedded or external PSC) are affected, but only if the vCenter server was upgraded from a previous version of vCenter Server, such as 6.0 or 6.5.
In this case, both VCSA as well as vCenter Server on Windows deployments are vulnerable.
Clean installations of vCenter Server 6.7 (embedded or external PSC) do not have this vulnerability.
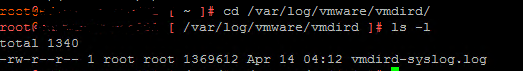
It is possible to verify if the current environment is impacted by this vulnerability, this is done by checking if the ACL is set to ‘Legacy Mode’ in the vmdir log file. The log file resides in the following folder:
On the vCenter Virtual Appliance
/var/log/vmware/vmdird/vmdird-syslog.log
In the log file you may see an entry like this:
info vmdird t@13991468466824664: ACL MODE Legacy
Important note: It is possible that, even though this entry does not show, the environment is still impacted. It is strongly advised to patch as soon as possible.
Mitigate Now!
If an environment is running a vCenter server 6.7 that has been upgraded from a previous version, update the affected vCenter server to version 6.7 U3f as soon as possible.
VMware has released the new version on the ninth of April, and it can be installed trough the VAMI as an update. The build number of this version is: 6.7.0.43000.
We have already pro-actively contacted our own customers impacted by this vulnerability. Most of the vCenter servers have already been patched over the course of the past weekend.
If your organization needs any help with mitigating this issue, feel free to contact us.
References
https://www.vmware.com/security/advisories/VMSA-2020-0006.html
https://kb.vmware.com/s/article/78543
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-3952
https://nvd.nist.gov/vuln/detail/CVE-2020-3952